Dropbox, EncFS and mounting pain
Posted on January 30, 2010
Painlessly mount EncFS encrypted folders with strong passwords using Gnome's keyring manager
The idea: Encrypt Dropbox data with EncFS
EncFS is a FUSE-based cryptographic file system that transparently encrypts files. It uses an arbitrary directory as storage for the encrypted files. This directory can be mounted to another directory which then provides access to the decrypted files.
EncFS is a good candidate for encrypting data in your Dropbox. Because it is file-based, changes to your decrypted files immediately get synchronized encrypted to your Dropbox. Another reason is EncFS's portability. It works on most Unix systems. Personally I use it to encrypt a specific folder in my Dropbox which I access from an Ubuntu Hardy, an Ubuntu Jaunty and a Mac OS X (Snow Leopard) machine.
Hint: If you share EncFS folders across multiple systems, create them on the system which has the oldest version of EncFS installed.
The problem: Mounting EncFS with strong passwords
Encrypting your data is a good idea, but it's only as safe as your password is strong. Using a strong password (24 or more characters, mixed case letters, numbers and special characters) makes mounting EncFS folders a pain, so you'll probably end up using a weak one if you have to type it manually.
There are solutions to automatically mount EncFS folder on login, namely pam-mount and pam-encfs, but these require that the EncFS folder has the same password as your local user account - which is probably a weak one compared to the password requirements mentioned above. As long as there is a certain physical barrier to your machine, local account passwords may be weaker as those used to encrypt data stored online, e.g. in your Dropbox.
The solution: Keyrings
Keyrings can be used to store strong passwords locally, encrypted with your local account password. Usually you then just login to your system and the passwords in the keyring are available for granted applications. In other words: Your strong EncFS password is protected locally by your comparatively weak local account password plus any physical access barriers.
Keyrings make it possible to automatically mount EncFS encrypted folders on login without the need to enter crazy long passwords.
Example: Gnome keyring
In this example the encrypted folder is ~/Dropbox/Encrypted and the mount point
for decrypted access to the files is ~/Private.
Detailed instructions for creating an EncFS directory can be found on the EncFS website. Here is a quick start:
$ mkdir ~/Dropbox/Encrypted
$ mkdir ~/Private
$ encfs ~/Dropbox/Encrypted ~/Private
> ... enter password ...
$ mount
...
encfs on /home/username/Private type fuse.encfs (...)
...
$ fusermount -u ~/Private # unmount
Put the EncFS password into the keyring
First we need to put the EncFS password into the Gnome keyring. For that task we need the command line tool gkeyring.
$ python gkeyring.py --set -n "Dropbox Private" -p encfs=dropbox --keyring login
> Password: <enter EncFS password here>
The option -p encfs=dropbox has no technical meaning. It is only used to
query the key later.
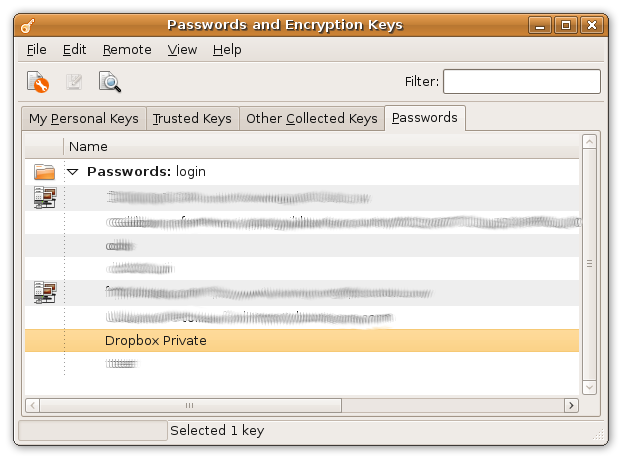
This new password should be visible in Seahorse now:
Mounting the EncFS folder with a Python script
Now we use a Python script which connects to the keyring to get the EncFS password and which then uses the password to mount the EncFS folder in the Dropbox:
#!/usr/bin/python
import os.path
import subprocess
import sys
import gtk
import gnomekeyring as gk
# paths constants:
PATH_ENCRYPTED = os.path.expanduser("~/Dropbox/Encrypted")
PATH_DECRYPTED = os.path.expanduser("~/Private")
# get the encfs-dropbox item:
try:
items = gk.find_items_sync(gk.ITEM_GENERIC_SECRET, {"encfs": "dropbox"})
item = items[0] # clean up your keyring if this list has multiple items
except gk.NoMatchError:
print("no entry in keyring")
sys.exit(1)
# run encfs:
cmd = ["encfs", "-S", PATH_ENCRYPTED, PATH_DECRYPTED]
p = subprocess.Popen(cmd, stdin=subprocess.PIPE)
err = p.communicate(input="%s\n" % item.secret)[1]
# either there is an error or we are done:
if err:
print(err)
sys.exit(1)
f you run this script, you'll be prompted to grant access to the "Dropbox Private" password:

Automount on login
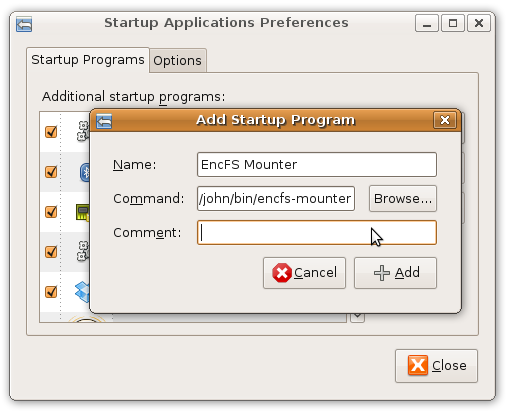
The final step is to add this script to the list of start-up applications via Menu -> System -> Preferences -> Startup Applications:
That's it. If you've spotted some errors or in case you have problems with these instructions, just drop a comment below.